
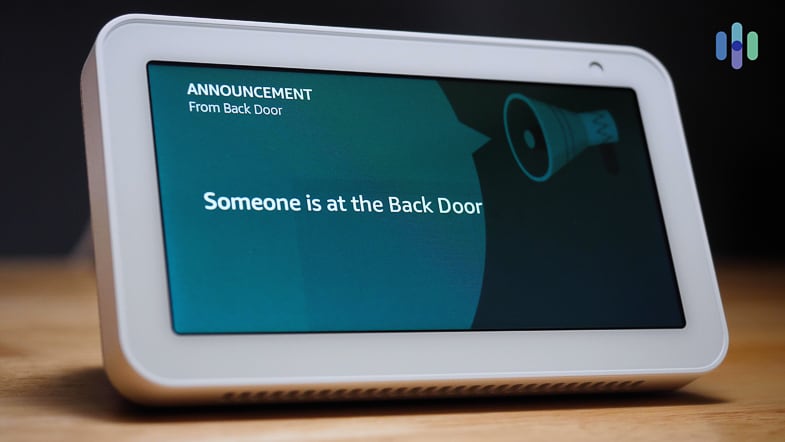
Attackers can force Echos to hack themselves with self-issued commands
4.8 (540) In stock

4.8 (540) In stock
Popular “smart” device follows commands issued by its own speaker. What could go wrong?

New Loop DoS attack may target 300,000 vulnerable hosts

Cyberattacks Are a Nuisance, Not Terrorism

Exploring Prompt Injection Attacks, NCC Group Research Blog

How Apple and Security Flaws Led to My Epic Hacking

Attackers can force Echos to hack themselves with self-issued commands
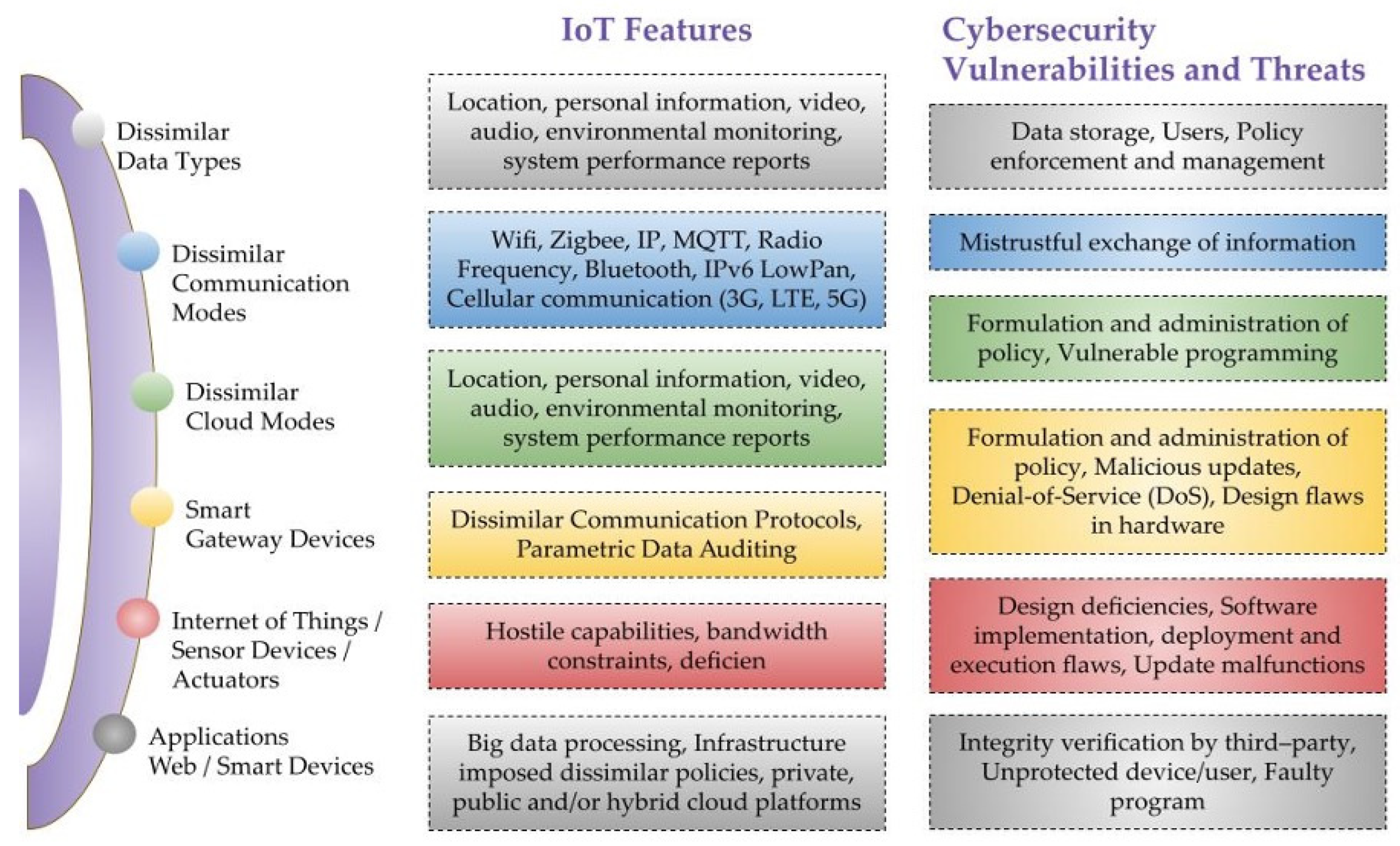
Sensors, Free Full-Text
How Hackers Outwit All Efforts to Stop Them: It's a Cyber Pandemic.
Best Home Security Systems That Work with Alexa in 2024

Hacking Auto-GPT and escaping its docker container
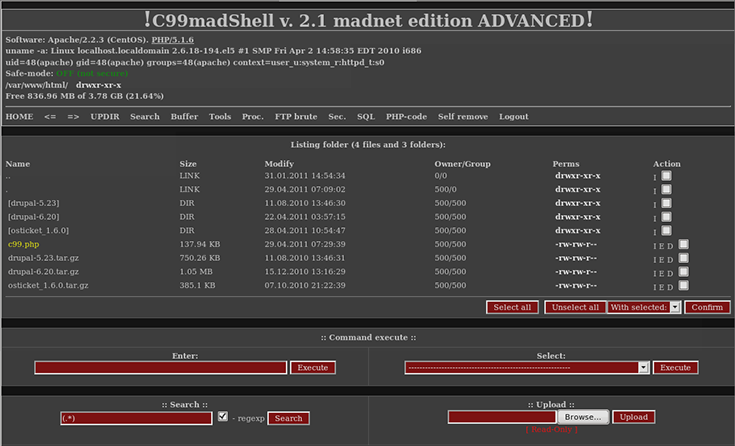
What is a Backdoor Attack, Shell & Trojan Removal
How would you hack me? As someone trying to protect themselves, what could I do that might make it harder/not worth it? (I know 100% secure is impossible) How do you personally
Hack I.T.: Security Through Penetration Testing T. J. - HackBBS

Hacking exposed mobile by hatty-ebooks - Issuu